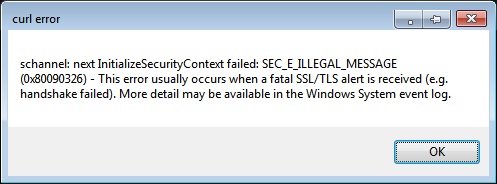
With the latest Windows update, released in October, there is often a particular problem regarding a network error. The message shows the error message "SEC_E_ILLEGAL_MESSAGE" which, in this new article, we will help you understand how to solve.

First of all, it appears when trying to make SSL and TLS connections on client and server. At the time of connection with the remote server, there are many users who, starting from the period considered, have begun to send reports regarding the inexplicable malfunction.
The patch released by Microsoft in October was then subject to correction by the same company from Redmond, which thus met what are, rightly, the needs of its users. This not before the confirmation of the objective existence of the problem by Microsoft itself. The problem unfortunately occurred later, specifically, to the update corresponding to the patch of the current month, showing the code KB5018427, as the company stated.
Index
- 1 Handshake between SSL and TLS protocols
- 2 The server connection problem and the systems affected by the SEC_E_ILLEGAL_MESSAGE error
- 3 Correction of SEC_E_ILLEGAL_MESSAGE problem
- 4 Installation and perspectives for other cases
Handshake between SSL and TLS protocols
The error from the SEC_E_ILLEGAL_MESSAGE message is due to an anomaly in the handshake procedure , again with reference to the SSL protocols, acronym for Secure Sockets Layer (Level of secure sockets), and TLS, which instead stands for Transport Layer Security ( Transport layer security). There are so many applications that use these protocols.
Among the same, there is also the security protocol, with regard to surfing the net, Https. This is the same protocol that initiates the asymmetric encryption system. It is used to ensure security in the exchange of data between client and server and vice versa. During the aforementioned handshake, the two communicating parties exchange data and thus aim to set common parameters regarding encryption, speed, compression protocols, error control, and several other common schemes.
In this way, cryptographic algorithms are established in the aforementioned bidirectional dialogue, which will be used together with the session keys (also established in the same dialogue). In fact, every time a user, during web browsing, connects to an Https page, the handshake process is activated, and therefore it is the browser that begins to communicate with the remote server and requests all the data and contents available for viewing. . The two devices will then recognize each other and the vehicular protocol for the exchange of information will be established. It is at the end of the process that the graphic contents displayed will appear, expected from the web page (with Https security protocol, distinct from simple Http, also used in web communication).
The server connection problem and the systems affected by the SEC_E_ILLEGAL_MESSAGE error
Microsoft patch KB5018427 from October 2022 makes itself responsible for sending multiple frames into a single input buffer. The procedure gives rise to the anomaly we have talked about and which comes from the party sending the data first, that is, in the input that our system will send under these conditions. For this reason we will not obtain permissions to view the web page in question and the error will appear:
SEC_E_ILLEGAL_MESSAGE
There are many systems affected by the error, practically all versions of Windows Server, starting from Windows Server 2008 R2 SP1, up to Windows Server 2022. And this only for the server side, in communication. For the client side, we'll have just as many systems on the list, starting with Windows 7 SP1, all the way up to Windows 11 22H2.
Correction of SEC_E_ILLEGAL_MESSAGE problem
Once the problem is framed, what it is and what it is due to, we can proceed with the resolution, based on the indications that the same parent company, Microsoft, has provided.
The indications refer, of course, to the download and installation of a further update capable of solving the SEC_E_ILLEGAL_MESSAGE problem . The latter, however, will not be found in Windows Update which can be accessed from a PC, but in an extraordinary section where the user will have to connect and manually download the necessary out-of-band update. The online section we discuss is Microsoft Update Catalog, and you will find updates at this link .
On the page in question you will find many types of updates and there is a special search bar to find them. To find what interests us in this case, type the code KB5020387 in the search bar if on our computerWindows 11 21H2 is installed. For other systems we will have a code variation. KB5020448 is valid for Windows 7 SP1 and Windows Server 2008 R2 SP1, KB5020449 for Windows Server 2012, while for Windows 8.1 and Windows Server 2012 R2 we will need the code KB5020447. Still, in continuation, always from the oldest system to the most recent one, for Windows Server 2019 and Windows 10 Enterprise LTSC 2019 you will need the code KB5020438. The user who has one of the following systems: Windows 10 20H2, Windows 10 21H1, Windows 10 22H1 and Windows 10 Enterprise LTSC 2021, will need the code KB5020435. Finally, for Windows Server 2022, the corresponding code for which a specific patch KB5020436 has been released .
Installation and perspectives for other cases
Once the search has been launched, just click on the result that will appear on the screen to start the download and installation of the patch to resolve the SEC_E_ILLEGAL_MESSAGE error .
Unfortunately, in addition to the operating systems already mentioned, it seems that other operating systems, outside the aforementioned list, also encounter problems. Not surprisingly, Microsoft said it is currently working to develop a specific patch. That reported peer fix is currently not compatible. Microsoft will certainly do it as soon as possible, and the patch considered will not be long in coming out. In the meantime, in case of other specific error messages, since it is not something generalized for Windows, there is a fairly exhaustive session of Chrome that talks about it, with all the procedures. You can find it at the following link .